The Snowflake Breach: How Missing MFA Handed Attackers the Keys to Everything
What Happened
Starting in late May 2024, a wave of high-profile companies discovered that attackers had walked straight into their Snowflake cloud data environments using stolen credentials. No zero-days. No exotic malware. Just a username, a password, and an open door.
The victim list tells you everything about the blast radius: Ticketmaster (560 million records gone), Santander Bank, and AT&T, where attackers pulled call and text metadata on approximately 109 million customers before anyone noticed. The group behind it, Scattered Spider, wasn’t doing anything technically impressive. They were doing something operationally effective, which is worse.
The thread connecting every compromised account: MFA was not enforced.
The Attack Chain
This is not a complicated sequence. That is exactly what makes it dangerous.
- Infostealer lands on an employee endpoint. Keylogger or credential-harvesting malware siphons saved browser passwords silently. No alert fires.
- Credentials are harvested and staged. Username and password pairs are exfiltrated to attacker infrastructure, sometimes sold, sometimes used directly.
- Attacker identifies the target platform. Snowflake login pages are publicly accessible. No reconnaissance required beyond knowing the org uses it.
- Credential spray runs against the login surface. Automated tooling tests the full dump. Accounts without MFA return an authenticated session immediately.
- Gap found. Attacker walks in. One account without MFA enforced is all it takes. The login looks identical to legitimate access.
- Queries run. Data pulled. Exfiltration complete. Cloud data platforms centralize enormous datasets. A single session with broad access can yield millions of records in minutes.
How They Got In
The attackers didn’t find a flaw in Snowflake. Snowflake itself wasn’t breached. The credentials they used had already been harvested, most likely via infostealer malware that siphoned saved passwords off employee endpoints weeks or months earlier. By the time the attackers showed up at the login page, they already had valid usernames and passwords. The only thing standing between them and terabytes of sensitive data was MFA, and for a significant number of accounts, that control simply wasn’t there.
With password-only authentication, their logins looked like routine access. No exploits firing, no lateral movement alerts, no anomalies. Just someone querying a data warehouse. The activity blended in because it was indistinguishable from legitimate use.
Once inside, the math was brutal. Cloud data platforms centralize enormous datasets by design. One compromised login on an account with broad access means one credential becomes one exfiltration event at massive scale.
This is why the attack pattern worked:
- Credentials were already burned via infostealer infections on employee machines
- No MFA meant no second factor to defeat, so stolen passwords were immediately usable
- Centralized data = concentrated risk, single-account compromise yields outsized damage
- Legitimate credential use looks normal, which delays detection and response
This isn’t a 2024 problem that got solved. This pattern is still the dominant attack vector in 2026. Identity misuse has lapped vulnerability exploitation as the path of least resistance. Attackers go where defenses are weakest, and authentication gaps keep giving them somewhere to go.
The Fix Is Not Complicated
That’s the part that stings. The defenses here aren’t bleeding-edge or expensive. They’re foundational, and the foundational stuff wasn’t in place.
Enforce MFA. Non-negotiable. Mandatory MFA on every account, especially administrative and externally accessible ones, would have stopped every unauthorized login in this incident. A stolen password without the second factor is just a string of characters. It buys attackers nothing.
Integrate with a central identity provider. Connecting cloud environments to Azure AD, Okta, or equivalent gives you conditional access policies, the ability to block risky login patterns, and forced step-up authentication when something looks off. You need policy enforcement, not just availability of MFA.
Treat your endpoints as the real perimeter. Infostealer malware is where these credentials originated. If your endpoint detection isn’t catching commodity stealers, you’re feeding attackers a credential pipeline. Scan regularly. Take infostealers seriously.
Basic hygiene closes the remaining gaps:
- Rotate passwords, disable inactive accounts, audit access regularly
- Monitor for unusual query volumes or large export activity in your data platforms
- Review which accounts have broad data access and cut down the blast radius before an incident forces you to
What This Looks Like in Your Logs
The attack is stealthy by design, but it’s not invisible. These behavioral indicators should be in your detection stack if you’re operating cloud data platforms:
- Authentication from a new ASN or geolocation with no prior history. Credential stuffing operations rarely originate from addresses that match a user’s normal login pattern. First-seen ASN on a successful auth is a high-signal event.
- Multiple successful logins across different accounts from a single source IP or ASN in a short window. Spray tooling moves fast. Sequential successes from one source is a pattern, not coincidence.
- Large query volume or data export within minutes of a first-ever login. Legitimate users don’t pull terabytes on their first session from a new device. High-volume exports shortly after authentication from an anomalous source should trigger immediately.
- Successful login on an account with no MFA challenge recorded. If your logs show an authenticated session but no MFA event in the sequence, that account either bypassed enforcement or enforcement wasn’t configured. Both are findings.
- Off-hours authentication on accounts that have never authenticated outside business hours. Attackers operate across time zones. Behavioral deviation on access timing is a low-cost, high-value signal when combined with other indicators.
None of these in isolation is a confirmed compromise. All of them together, or any one combined with a large export event, warrant immediate investigation.
Demo: Watching It Play Out
In our demo environment, the attacker starts with a credential dump for ApertureDataCloud. They try the obvious first: admin/admin. Denied.
Admin login attempt fails on ApertureDataCloud
Rather than stopping, they examine the site structure, intercept web traffic to map the authentication flow, and write a custom spray script to run the full credential dump against the login surface.
They quickly discover that MFA is enforced for some accounts. Logging in as carol triggers an MFA challenge immediately. The script notes it and keeps running.
MFA challenge fires for carol’s account
A few minutes later the script flags it: the nuck account returns AUTHORIZED with no MFA challenge. Every other account in the dump hit MFA BLOCKED. This one didn’t.
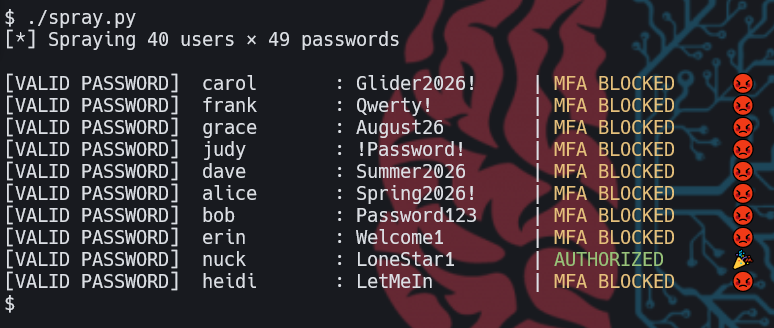
spray.py output: nuck authorized, all others MFA blocked
The attacker logs in as nuck without friction. The account has access to a confidential customer master export: names, SSNs, dates of birth, emails, account balances. They query it. They pull it. Exfiltration is trivial at this point because there’s nothing left to stop them.
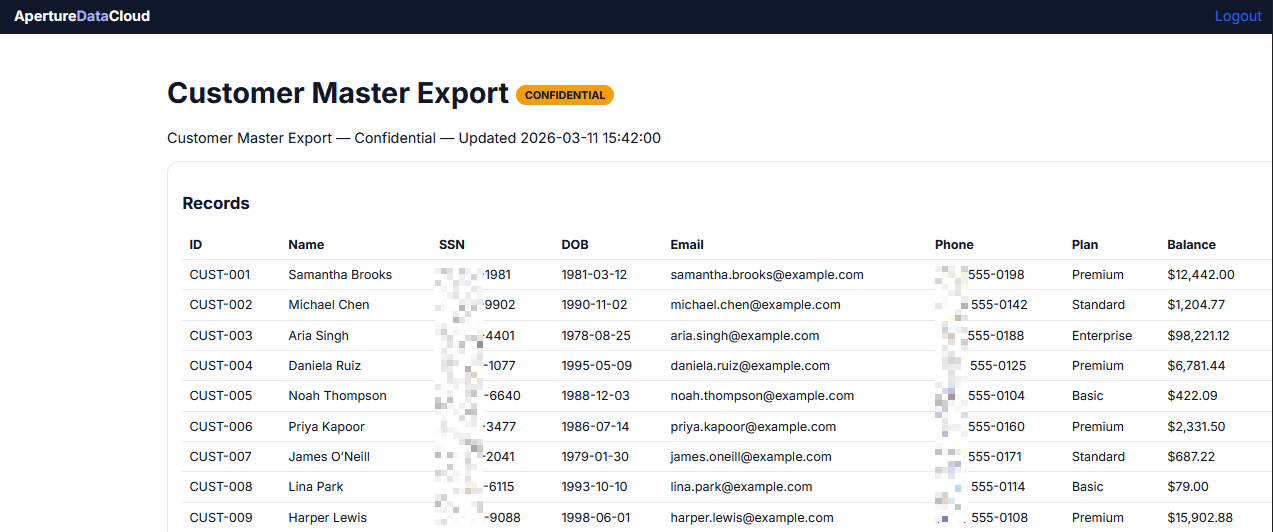
Attacker accesses the Customer Master Export after logging in as nuck
That’s the whole attack. Credential dump, spray, find the gap, walk in, take the data. The only meaningful control point was MFA, and it wasn’t enforced on that account.
The Bottom Line
Passwords get compromised. That’s not a theory, it’s an operational reality. Phishing, infostealers, credential stuffing, breach reuse, it happens constantly at scale. Relying on passwords as your sole authentication control in 2026 means you’re betting that none of your users’ credentials ever show up in a dump anywhere. That’s not a bet you can win.
MFA breaks the chain. A leaked password becomes useless if the attacker can’t provide the second factor. It’s the most asymmetric defensive investment available: low cost, high friction for attackers, minimal friction for users when implemented correctly.
Enforce it everywhere. Don’t leave gaps. One account without MFA is the one account they’ll find.
Identity gap detection is exactly what MILBERT was built for. If you want to know whether an attack like this would surface in your environment before someone else finds out, reach out to ThreatHunter.ai.